GitHub - kubernetes/k8s.io: Code and configuration to manage Kubernetes project infrastructure, including various *.k8s.io sites

GitHub - omerbsezer/Fast-Kubernetes: This repo covers Kubernetes with LABs: Kubectl, Pod, Deployment, Service, PV, PVC, Rollout, Multicontainer, Daemonset, Taint-Toleration, Job, Ingress, Kubeadm, Helm, etc.
Hierarchical structure of Deployment, ReplicaSet, and Pod (adapted from... | Download Scientific Diagram

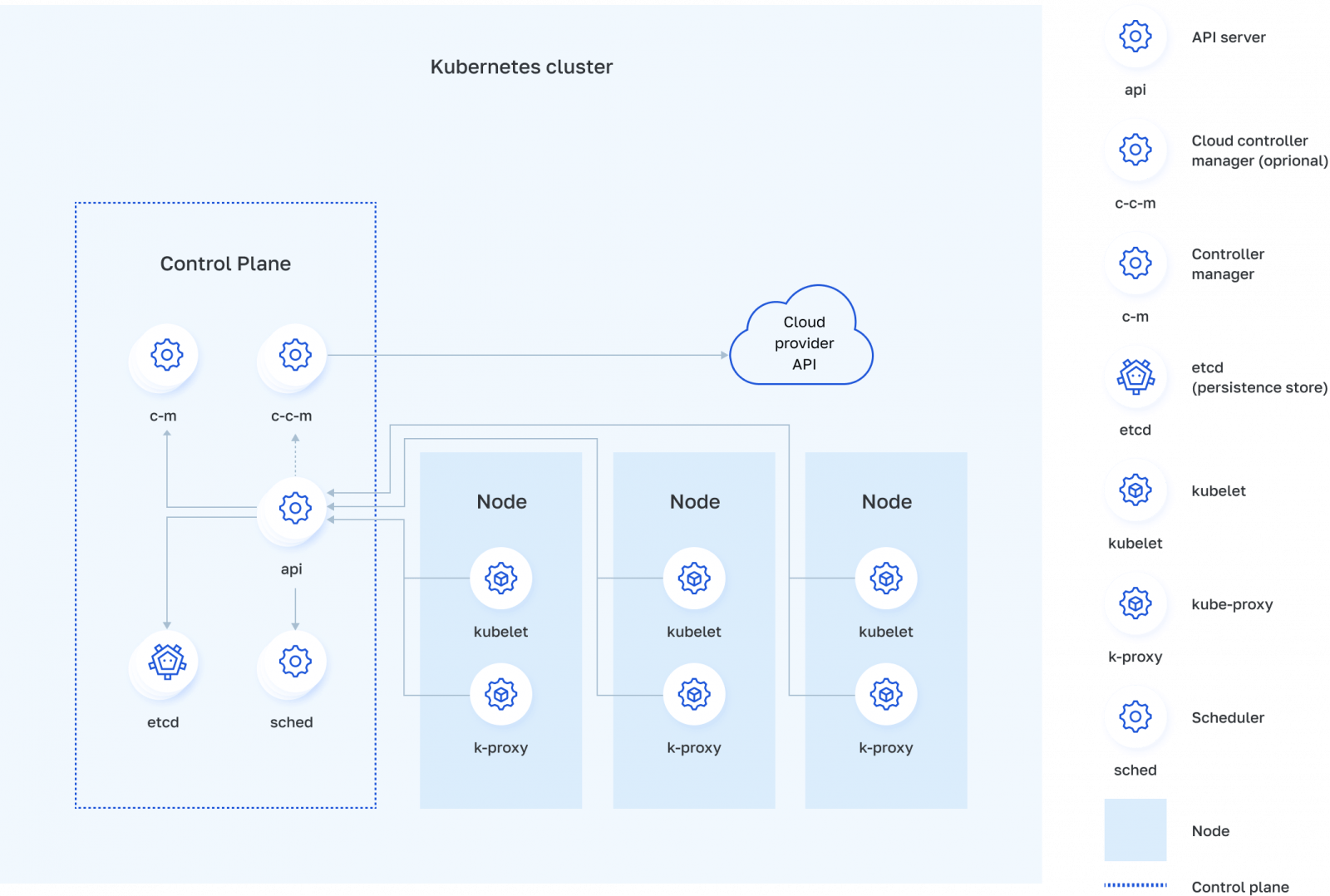
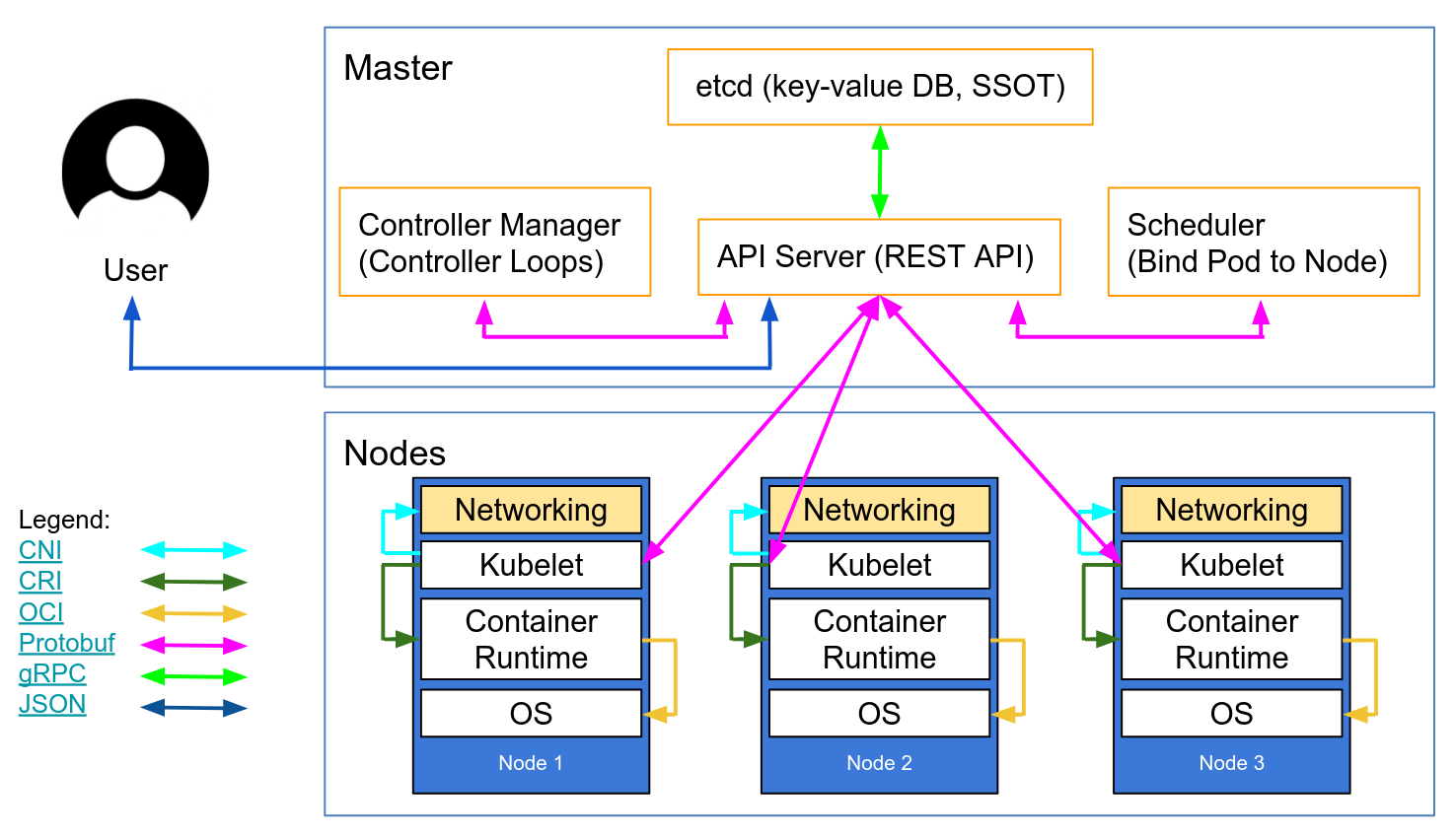
What is Kubernetes?. An Intro To The Open-Source Container… | by David Dymko | FAUN — Developer Community 🐾
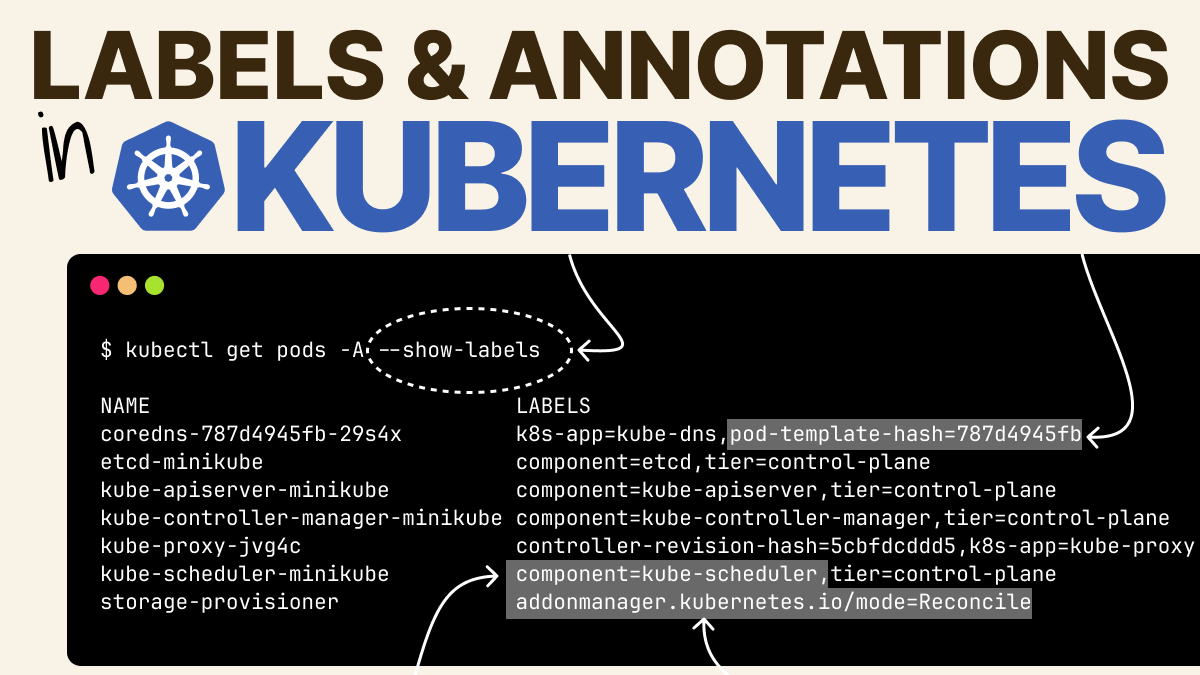
Daniele Polencic — @danielepolencic@hachyderm.io on X: "In Kubernetes, you can use labels to assign key-value pairs to any resources. Labels are ubiquitous and necessary to everyday operations such as creating services. However,

Kubernetes.io Blog: The Future of Cloud Providers in Kubernetes - General Discussions - Discuss Kubernetes